Two security researchers have demonstrated an easy way to attack the BIOS chips on millions of PCs in under two minutes, undermining all physical and software security and potentially allowing encrypted data including passwords to be stolen. The two suggest that this technique has most likely already been used by the US National Security Agency.
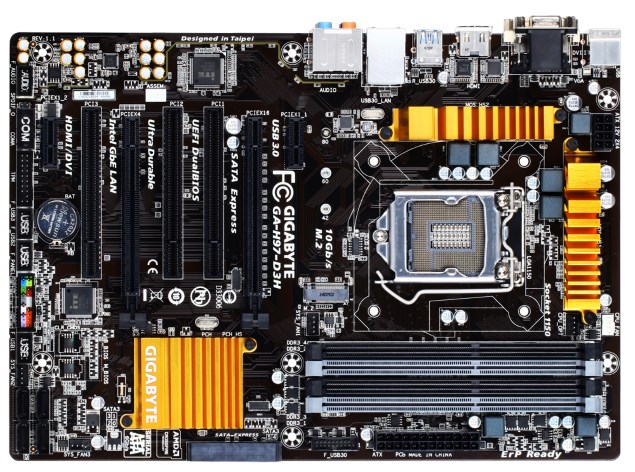
In a talk titled How Many Million BIOSes Would You Like to Infect at this year's CanSecWest conference, researchers Corey Kallenberg and Xeno Kovah showed how vulnerable the UEFI BIOS implementations on all modern motherboards are. The problem, they said, is made even worse because users rarely patch their BIOS chips when updates are released by manufacturers.
The UEFI BIOS on modern PCs is a miniature operating system itself, and is invisible to desktop antimalware programs. By taking control of it, attackers can either disable a PC entirely or subvert its functions. What's more dangerous is that direct access to data in memory is possible, which means attackers can extract encryption keys, passwords, and other data even when so-called secure operating systems are used.
No comments:
Post a Comment